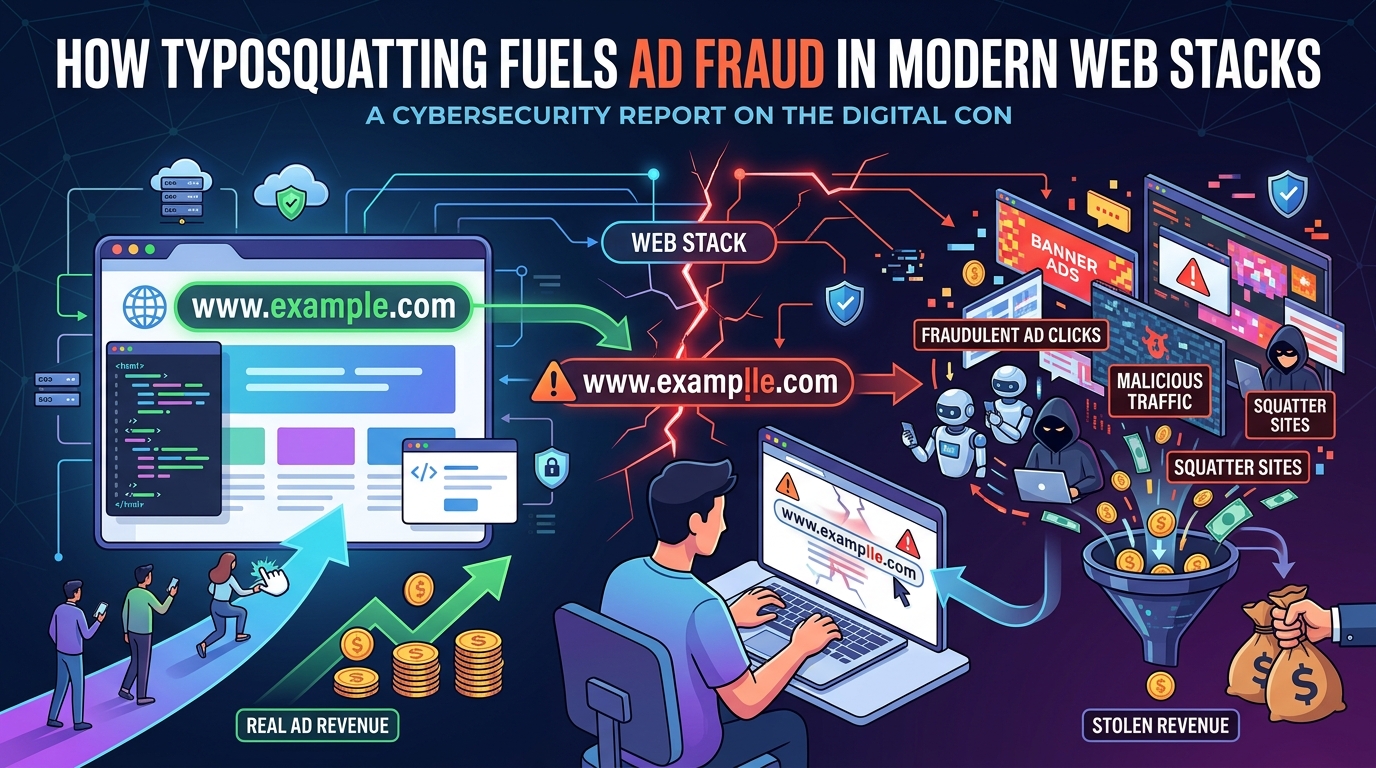
Fake Clarity-Style Scripts, Real Damage: How Typosquatting Fuels Ad Fraud in Modern Web Stacks
Your site can be compromised without a server breach, a leaked credential, or a broken firewall rule. All it takes is one typo in a third-party script include.
In 2026, most production websites ship with a small ecosystem of externally hosted JavaScript: analytics, tag managers, session replay, A/B testing, customer chat, personalization, payments, fraud detection, embedded widgets. These scripts run with the same privileges as your own frontend code—on every page, for every user, at scale. That’s why typosquatting paired with ad‑fraud script abuse has become one of the most effective “silent failure” attacks on the modern web.
This article breaks down how it works, why it’s spiking now, what it costs teams, and a practical playbook to detect and prevent it—especially in the AI‑assisted coding era.
What this means
Typosquatting
Typosquatting is when attackers register domains (or publish packages) that look almost identical to trusted names, but with tiny spelling differences that humans miss during reviews.
You’ve seen the pattern:
- clarity.microsoft.com (real product) vs clarity-microsoft.com (fake lookalike)
- cdn.segment.com (real‑style vendor domain) vs cdn-segment.com (fake lookalike)
Even if the fake domain isn’t an obvious “phishing” site, it can be a perfect delivery vehicle for malicious JavaScript.
Microsoft’s Clarity product and documentation are a good example of a legitimate mainstream tool that teams commonly install by pasting a snippet into the <head> of their site. That copy‑paste habit is exactly what typosquatters exploit.
Ad‑fraud script abuse
Ad‑fraud script abuse is when a malicious script runs in real user sessions and performs actions like:
- generating fake ad impressions or clicks
- redirecting traffic (sometimes only for certain geos/devices)
- manipulating session behavior (scrolling, clicks, events)
- fingerprinting users and beaconing data out
- loading additional payloads later (turning “ad annoyance” into a broader supply‑chain compromise)
This is not “just annoying ads.” Once a malicious third‑party script is running on your pages, you’ve effectively granted it a seat inside your frontend supply chain.
Why this is hot right now
Four trends make this threat unusually effective today:
- Everyone uses third‑party scripts. Analytics and product telemetry aren’t optional in many organizations—they’re baked into growth, UX, and revenue operations. Microsoft Clarity’s documentation literally guides teams to paste tracking code into the
<head>. - Modern web apps are script‑heavy. A single include in a layout template can execute across every route, every user, every time.
- Trust is inherited by default. Teams “approve” a vendor in a procurement sense, then treat anything that looks like that vendor as safe. Domain allowlists often get written from memory, Slack messages, or old tickets.
- AI‑generated code raises the odds of plausible mistakes. AI assistants can output “reasonable looking” script URLs that are subtly wrong. Developers in prototype mode paste first, verify later—and “later” often never comes because the app still works.
The result: an attacker doesn’t need to breach your servers. They just need your team (or a contractor, theme, plugin, or tag‑manager change) to paste the wrong snippet once.
The typical attack chain (and why it’s so stealthy)
- Attacker creates a lookalike domain or script path. They pick names that blend into dashboards and code reviews.
- A team member includes the wrong snippet, often through:
- copying from a blog/tutorial
- a contractor using “what worked before”
- a CMS theme/plugin adding “analytics”
- a tag manager change with weak governance
- an AI assistant suggestion that looks legit
- The script executes in production on every page where it’s included.
- Malicious behavior triggers, frequently conditional to avoid detection:
- only on mobile Safari
- only in specific countries
- only for new users
- only after a delay
- only when certain UTM params exist
- It goes unnoticed because the app still works—no downtime, no obvious broken UI, and metrics may even look “fine” because the attacker is careful not to disrupt core flows.
The blast radius: one bad include can taint your whole site
The frontend is uniquely fragile because third‑party scripts:
- run inside your origin context (same DOM, same page)
- can read what users type or click (depending on what you render client‑side)
- can inject new scripts dynamically
- can silently slow down performance and skew metrics
- can create reputational damage through redirects and spammy behavior
Even if the attacker’s first move is “just” ad fraud, the access level is the same access level you gave your own app code.
Real impact on teams
- Revenue loss: ad fraud drains budgets and pollutes attribution; redirect schemes can siphon high‑intent traffic.
- Data privacy exposure: session details, page content, and identifiers may be exfiltrated; third‑party scripts can beacon data to unexpected endpoints.
- Performance degradation: extra JS, extra network calls, delayed interactivity; “mysterious” Core Web Vitals regressions.
- SEO and reputation damage: sneaky redirects, injected spam, or cloaking behaviors; users losing trust after unexpected navigation.
- Compliance risk: if PII leaks through third‑party scripts, you may have disclosure obligations depending on jurisdiction and contracts.
How to detect it: a practical checklist
- Inventory every external script and domain.
<script src="…">domains- dynamically loaded script endpoints
- tag manager containers and their published versions
- Verify against official vendor documentation.
- Don’t validate by “it looks right.” Validate against the vendor’s official docs.
- Monitor unexpected network calls in production.
- new third‑party domains
- unusual beacon endpoints
- requests that only appear after user interaction or time delay
- Alert on new third‑party domains.
- Any new domain in production is a security event until proven otherwise.
- Track script changes (hashes, sizes, and behaviors).
- If a third‑party script changes unexpectedly, treat it as suspicious.
Prevention framework: turning this from a guessing game into policy
- Use Subresource Integrity (SRI) where possible.
- SRI lets you pin a cryptographic hash for external resources. If the file changes, the browser blocks it.
- Reality check: SRI is easiest when you control versioned assets (or self‑host the script). Many analytics vendors serve mutable scripts, which complicates SRI.
- Enforce a strict Content Security Policy (CSP).
- A CSP header declares what resources are allowed to load. Modern browsers block everything else.
- If your CSP only allows the exact legitimate domains, a lookalike domain won’t execute—even if it’s pasted into the HTML.
- Script pinning + approval workflow.
- Treat new third‑party scripts like new dependencies: require a ticket/change request, exact domain + path, approval record, and rollback instructions.
- Tag manager governance (least privilege).
- Restrict publish permissions.
- Require review for any new tag/vendor.
- Log every publish (who/what/when).
- Maintain an “approved vendor registry” that the tag manager can use.
- CI checks for suspicious domains.
- Lint for new external domains in HTML/JS.
- Block known typosquat patterns (hyphenated lookalikes, swapped words).
- Require an allowlisted domain registry for any third‑party includes.
Mini incident‑response runbook (frontend supply chain edition)
- Remove/disable the suspicious script immediately.
- Revert tag manager publish.
- Remove the
<script>include from templates. - Disable the plugin/theme module if it injected the script.
- Search for secondary payloads.
- Malicious scripts often load more scripts dynamically.
- Review recent network logs for follow‑on domains.
- Rotate exposed secrets.
- If the script had access to tokens, API keys, or session identifiers, rotate them.
- Review what was accessible client‑side.
- Audit traffic and behavior.
- Look for spikes in redirects, bounce rate, suspicious referrers, and odd geos.
- Compare before/after the include date.
- Notify as required.
- Legal/compliance assessment if user data may have been exposed.
- Partner notifications if attribution/ads were impacted.
- Postmortem + guardrails.
- Add CSP/SRI/CI checks so the exact failure mode can’t recur.
The “AI era” angle: how assistants can increase typosquatting risk
AI coding assistants are useful—but they optimize for “looks plausible” and “works,” not “is authentic.” Common failure modes:
- Plausible‑but‑wrong script URLs: a model may hallucinate a vendor CDN domain that sounds right.
- Prototype‑speed copy‑paste: the faster you iterate, the less time you spend verifying.
- Reviewers focus on functionality: the page loads, analytics fires, the ticket closes—nobody stares at a hostname.
Mitigations that actually work:
- Trusted‑domain linting in CI: fail builds when new third‑party domains appear without approval.
- Approved registry for script URLs: engineers can only pull scripts from a curated list.
- Human review for every new third‑party include: not “LGTM, it works.” Specifically: “Is this domain official and correct?”
This flips AI from “risk amplifier” back into “speed tool”—because you’re enforcing authenticity mechanically.
Key takeaway: treat frontend scripts like production dependencies
Typosquatting + ad‑fraud script abuse succeeds because it exploits a gap between how teams think they manage vendors and how they actually manage script execution. A single wrong domain can grant an attacker execution on every page, for every user—without breaking your site and without triggering traditional breach alarms.
Defensive goals:
- Know every third‑party script you run.
- Restrict what’s allowed to execute (CSP).
- Lock what shouldn’t change (SRI where possible).
- Automate review so “one typo” can’t ship.
That’s how you turn a silent, scalable compromise path into a blocked request in the browser console—where it belongs.




